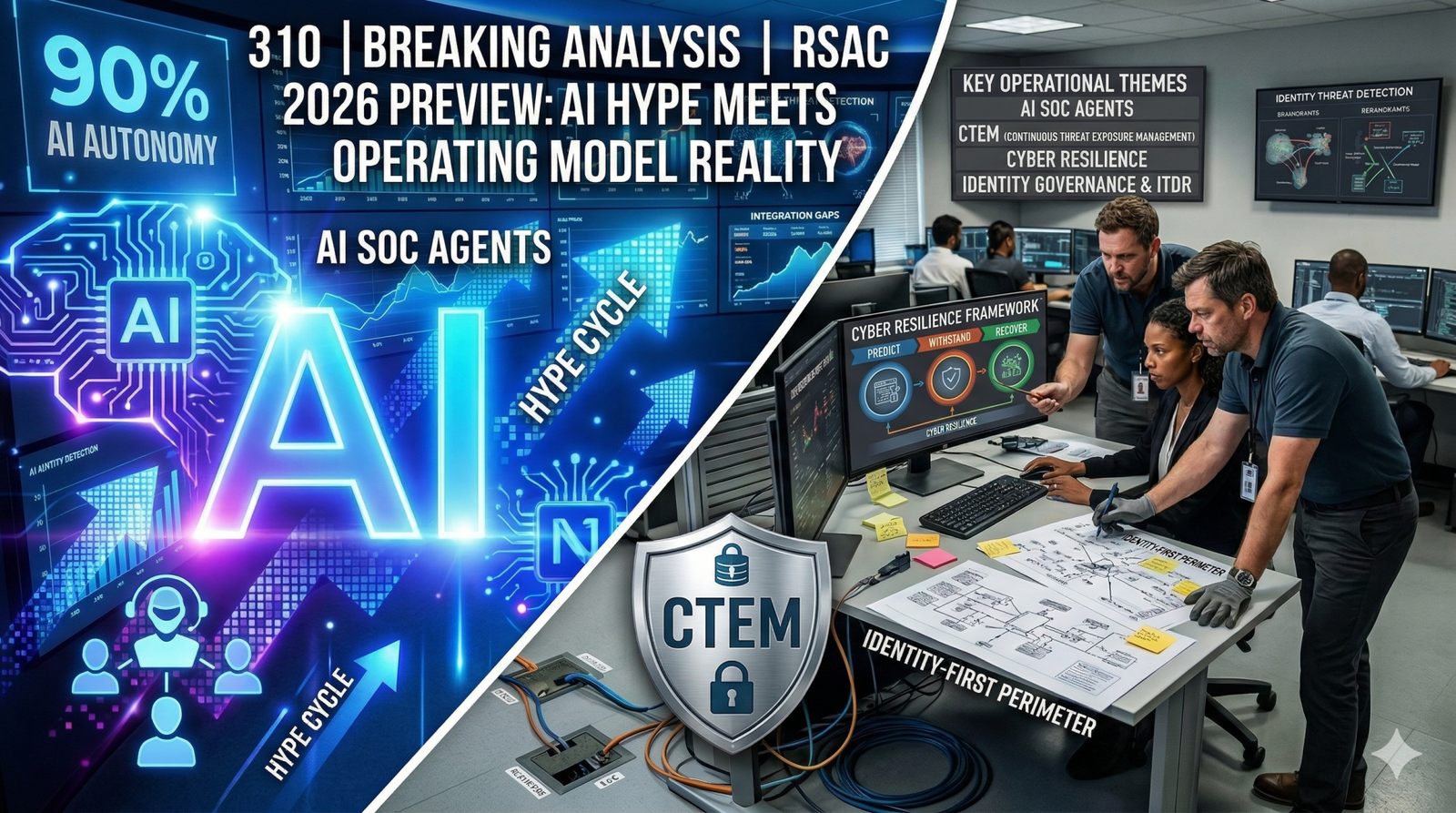
We all know that the RSAC 2026 cybersecurity conference this week in San Francisco goes to be a synthetic intelligence-heavy show. And though we’re going to listen to the “AI will change all the things” narrative, our premise is that security leaders are being asked to place AI into operation in an environment where complexity is rising faster than control.
Organizations are still struggling to consolidate the sprawl of tools of their security stacks and at the identical time apply zero-trust principles. To avoid AI becoming one more layer, organizations must tie AI to clear outcomes and integrate intelligence into operating processes. Enterprise Technology Research survey data captures the challenge. At the very least 90% of organizations say they’re leveraging AI somewhere of their security stack, but 75% are applying AI to lower than 10% of their security portfolio.
And that gap quantifies the degree to which AI is present, but not yet scaled. Most deployments are narrow or tactical and constrained by the identical blockers: reliable data access, integration across tools, governance and trust.
The AI security operations center conversation will even dominate RSAC with increasingly automated triage, investigation, things resembling isolation and patching and the like. But agents will succeed or fail on foundations resembling telemetry, quality, identity controls and exposure management hygiene, and, after all, recoverability. As cybersecurity expert Jon Oltsik wrote in his RSAC preview, the agenda for RSA 2026 needs to be approached with curiosity and optimism, but in addition suspicion and, after all, a plan. The conference goes to be filled with platform claims across AI SOC, exposure management, identity and cyber resilience. But the sensible query for chief information security officers is where AI reduces time to detect, time to reply, and operational friction without increasing risk.
And where it simply adds one other tool that the team can’t integrate, govern or measure, that needs to be avoided. On this week’s Breaking Evaluation, we collaborate with Jon Oltsik to arrange you for RSAC 2026 and highlight five top trends that he believes CISOs should monitor at this yr’s conference.
RSAC’s theme this yr is “The Power of Community,” and the timing is slightly ironic given how much of the conference buzz goes to be about AI agents. The safety industry has develop into more collaborative during the last decade – competitors share more threat intelligence and practitioners work together greater than they used to. Now there’s a brand new dimension: machine-based agents acting on behalf of humans.
The appropriate option to square the circle is to treat agents as a complement to what security teams already do. Sometimes they replace people, sometimes they augment people, but they extend the community slightly than compete with it. The community and collaboration have at all times been there in cybersecurity, to various degrees. Agents are one other tool inside that community that may extend, enhance, and complement human work.
The sensible implication is the theme works if the main focus stays on how AI helps the community do higher work, and the way it helps practitioners as individuals and teams. When AI is used that way, the ironic theme becomes greater than marketing.
The rise of the AI SOC: Progress meets caution
The AI SOC might be one among the loudest conversations at RSAC 2026. Vendor messaging is moving beyond copilots that help analysts, toward agents that may tackle real SOC work resembling triage, investigation, containment and even remediation steps resembling isolating hosts and initiating patch workflows. The direction is alluring, however the gap between promise and operational reality still lingers.
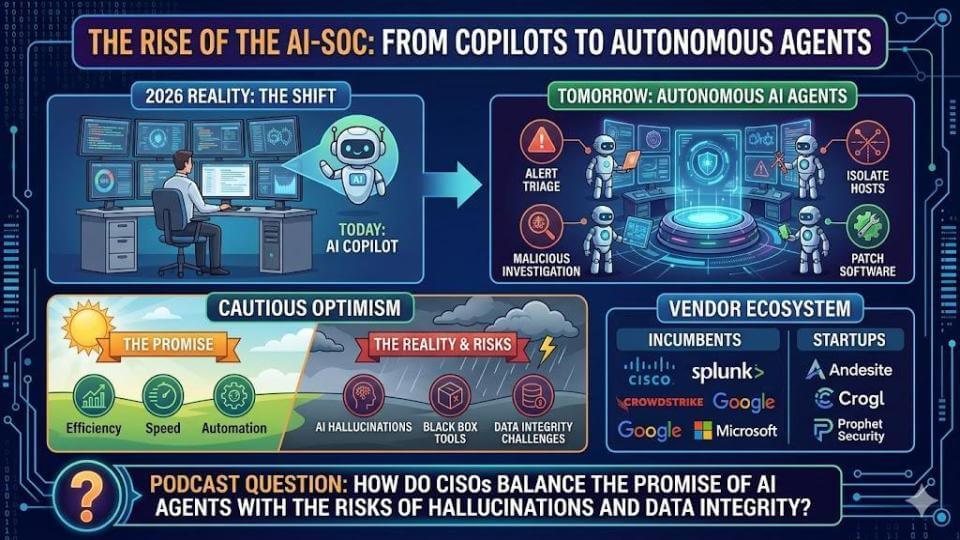
Essentially the most credible progress is coming from focused use cases. Startups have generally picked a slice of security operations and gone deep with things resembling alert triage as an obvious example. SOCs drown in alerts. Historically, even strong teams could only treat a small fraction of them. We imagine AI-driven triage can push that number dramatically higher – from the old 15% to twenty% range to something closer to 90% to 95% in the perfect cases. That’s meaningful to a gaggle of pros which might be constrained by time, attention and data volume.
Security teams remain cautious by nature. The human-in-the-loop mindset continues to be deeply embedded of their psyche. In our view, the sensible approach is to evaluate where automation helps most – where processes are inefficient and where teams are bottlenecked by data. That needs to be the start line for AI SOC adoption.
The near-term reality is that implementation is bifurcated. Some capabilities might be added onto existing platforms and workflows. Other capabilities will emerge as more AI-native approaches. The market is within the early phases, however the innovation is moving fast, and RSAC might be an excellent place to separate signal from rebranding.
MSSPs: The fastest path to ‘automation at scale’
Essentially the most aggressive AI SOC deployments may come from managed security service providers, for an easy reason that the MSSP business has thin margins and scaling by hiring and training people doesn’t work. It’s especially hard when everyone seems to be competing for a similar talent.
This creates strong economic pressure for MSSPs to adopt AI and process automation quickly. Our expectation is that enormous MSSPs resembling Arctic Wolf Networks Inc., Expel Inc. and LevelBlue Inc. might be amongst essentially the most aggressive in deploying automation because doing it well expands margins and grows market share. That may be a path many buyers and vendors overlook, and it is going to be price listening closely to what these providers are saying at RSAC.
Nick Schneider, CEO of Arctic Wolf, is coming on our CEO series, and probing this specific point – how far they will push automation while managing trust and liability – needs to be high on the query list.
CTEM and the mandate for credible data
Continuous threat exposure management or CTEM will get attention at RSAC because snapshot scanning and static vulnerability doesn’t delay in a world that moves at machine speeds. The premise is that security teams desire a clearer picture of assets, configurations, location, vulnerabilities, ownership and business criticality, tied to threat intelligence and adversary tactics so that they can prioritize.
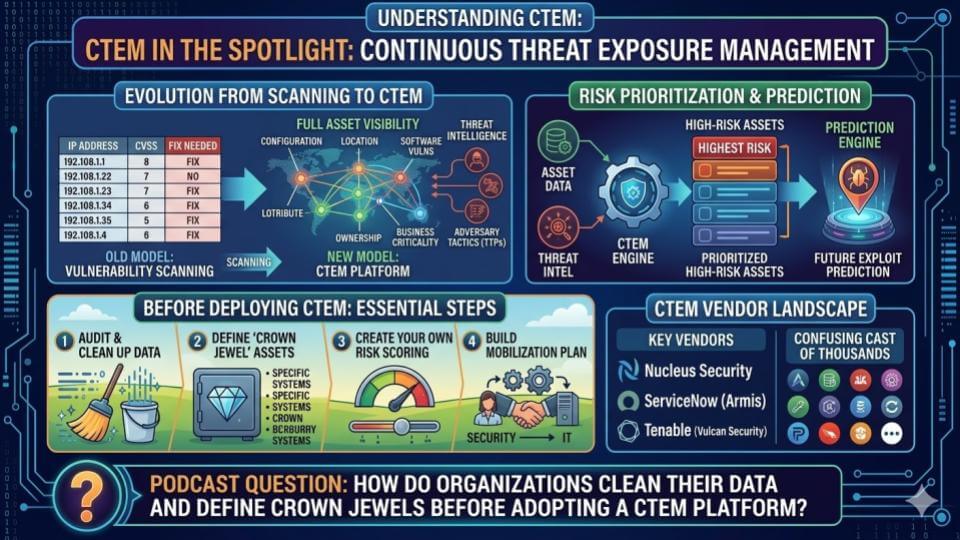
The catch is CTEM lives or dies on data. The primary questions are boring but necessary: Is the info accessible, available and in a format that might be used effectively? Once the info is usable, the following step is context : Which assets are critical, what are the critical paths to those assets, who has access, are systems configured appropriately, and is MFA in place? That upfront work is commonly ignored as people jump to tooling.
CTEM also doesn’t work well as a generic product drop-in. It must be customized by industry, use case and organization. The vendors that thrive might be people who acknowledge this reality and will help operationalize the work, not only sell a platform.
When CTEM is finished right, the advantages are tangible as follows:
- Higher confidence in risk scoring – distinguishing “vulnerable” from “exposed;”
- Predictive evaluation based on what adversaries have exploited previously and sure future paths;
- Higher alignment with information technology operations – replacing “listed here are 1,000 exposures, patch now” with prioritized remediation that maps to business criticality.
The opposite necessary point is that “get your data house so as first” generally is a limiting strategy. The safety world has been on the info security journey for years – discover data, classify data, then apply the fitting controls. The truth is there is simply too much data and it’s growing too quickly.
AI becomes an accelerant for quality discovery and classification, and it hastens the trail to raised controls. Waiting for perfect data clarity doesn’t make sense. The sensible approach is working in parallel. In other words, construct the info foundation while using AI to shape, cleanse and deal with the info that matters for the duty at hand.
Cyber resilience: A capability, not a product
Cyber resilience is one among those terms the industry likes to market, nevertheless it only becomes useful when it will probably be operationalized. The NIST definition helps break resilience into phases: Anticipate, withstand, get well and adapt. And it forces teams to think beyond a single control or a single tool.
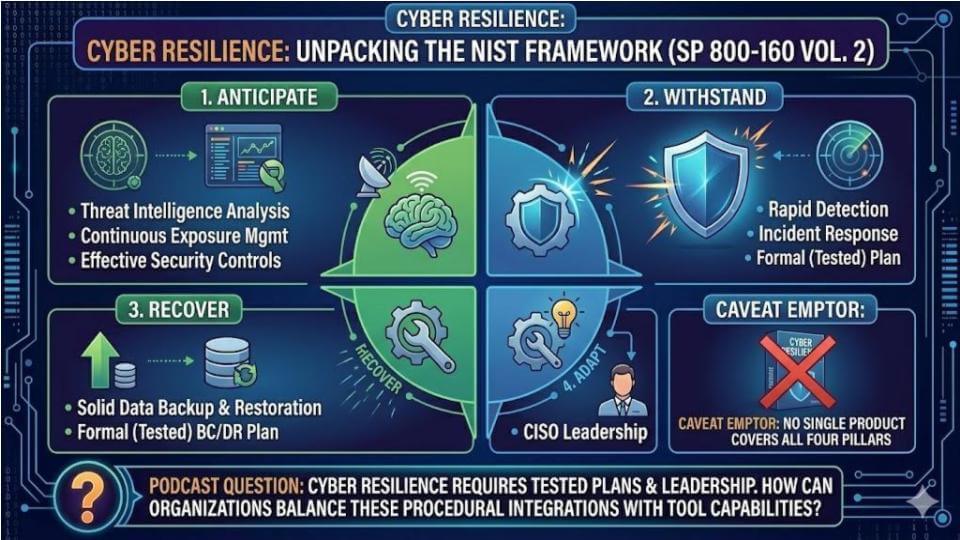
The primary red flag is that if any vendor says “we sell a cyber resilience product” – run, don’t walk. As if it’s a product you may buy off the shelf. A tool may support one a part of the framework, but cyber resilience is the final result of multiple capabilities working together.
The appropriate place to begin is the business. Discover what systems and business processes must remain resilient. Healthcare is an excellent example because the main focus isn’t “hospital resilience,” it’s clinical resilience – treating patients. If systems go down, the organization still has to operate, even when which means paper and pencil. That mindset helps deal with the trail to a desired final result.
From there, step through each phase of the NIST framework:
- Anticipate – understand threat intelligence, who’s attacking and the way, apply frameworks like MITRE ATT&CK, do detection engineering and tune controls;
- Withstand – use segmentation so compromise in a single area can’t reach crown jewels elsewhere, and strengthen the power to detect and respond quickly.
- Get well – deal with the mechanics of getting back online fast, including immutable backups and proven recovery processes; with minimal loss for prime value data.
- Adapt – learn from incidents, tune technology, refine procedures and make targeted investments with CISO leadership driving the changes.
A key learning from experts is that resilience is determined by planning and testing. Business continuity and disaster recovery works when it’s practiced, however the worst-case scenario is at all times the one which wasn’t planned for. 9/11 is a reminder in that many financial firms were diligent about BC/DR with redundant sites and connectivity, but they didn’t anticipate the simultaneous impacts of individuals not being available and infrastructure crushed across multiple locations. Resilience means excited about those scenarios, planning for them and testing the plan.
The north star just isn’t a product portfolio. It’s the power to maintain critical processes operating through disruption, limit blast radius when systems are compromised, and restore operations quickly with confidence. In our view, that’s the mindset CISOs should use when evaluating “cyber resilience” claims at RSAC.
Identity is the perimeter: Governance, no passwords and identity-first detection
In 2023, the theme of the conference focused on an identity crisis. Identity is at all times center stage at RSAC 2026 since the perimeter is gone and has been for quite a while. The old idea of digging a moat around a network has long been obsolete in a world of cloud apps, distant data and distributed access. Identity becomes the safety perimeter, and the most important query we pose and are watching at RSAC is where identity is definitely advancing versus getting repackaged.
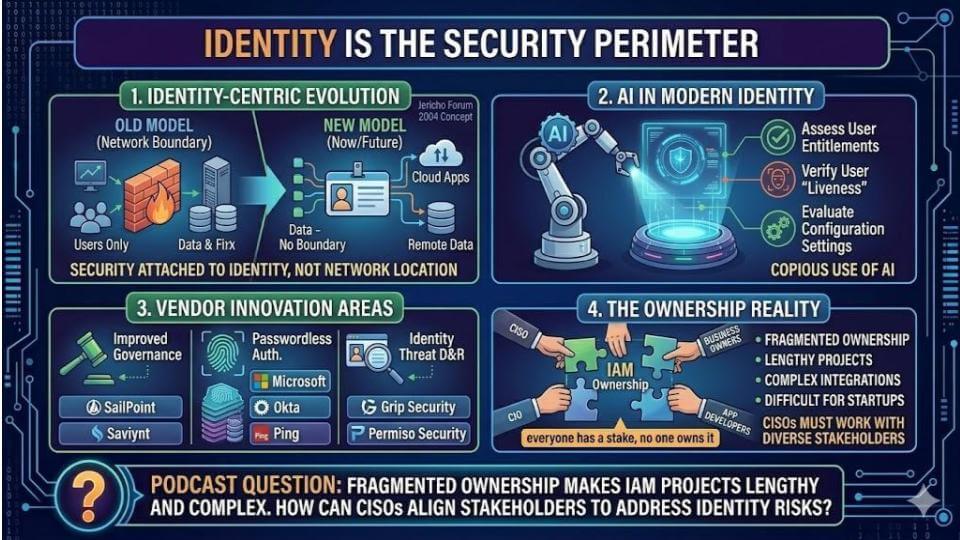
One change is organizational. Previously, security had a seat within the room when identity got here up. Now security has a seat on the table and a primary voice. Identity is pulling security into development, IT operations and business processes because you may’t bolt it on later.
The sensible progressions we advise are as follows:
- Identity governance: Who must have access to what? The early approach was a checkbox exercise where security presents business owners with lists of users and asks, “Should they’ve access or not?” Business owners didn’t have time to deeply consider the implications and that approach didn’t scale; nor was it personalized. The chance now could be to make use of AI and assess entitlements repeatedly – who’s accessing what, whether that matches their role, whether their role modified and whether access needs to be revoked. This can be a strong fit for agents since it’s high-volume and repetitive, and rules plus context might be learned from behavior over time — and alter dynamically.
- Passwordless: The plain query is why passwords still exist in 2026. The technology is here – FIDO2, passkeys – and the momentum is shifting toward mandate. The consumerization of identity is coming to the enterprise. People use passkeys for banking and other consumer workflows, after which come into the enterprise asking why internal systems are behind. Identity often enters through the back door that way. We agree with Larry Ellison: Passwords are a terrible idea.
- Identity threat detection and response: The main target is moving toward identity-centric attacks and detection. Identity attacks are dominating because stealing or finding passwords is commonly easier for attackers than exploiting software vulnerabilities. That pushes enterprises toward behavior-aware detection – understanding what “normal” looks like for a user within the context of day by day work and flagging deviations. This is expounded to UEBA, or user and entity behavior analytics, but the purpose is security teams need higher identity telemetry and higher response vectors when credentials are abused.
- Human risk management: Training becomes individualized slightly than broadly applied across a company or department. AI can discover who’s more prone to click phishing links and tailor training and “nudges” to how that person learns – video, reading, short prompts – and deliver it within the moment when behavior needs to vary.
The perfect final result in our view is an identity program that’s not only authentication and provisioning. It’s governance, behavior and response, tied into business process and operations. And if the industry is serious about eliminating passwords, the goal is easy that computers should know who you’re after they see you.
ETR data: AI adoption is steadily increasing but still shallow
Let’s take a fast detour into Enterprise Technology Research’s pre-RSAC survey data, which shows why RSAC 2026 goes to feel like an AI conference, though adoption continues to be uneven. The most recent survey shown below has 517 respondents, and the query posed is: What percentage of a company’s security tools leverage some type of AI or ML?
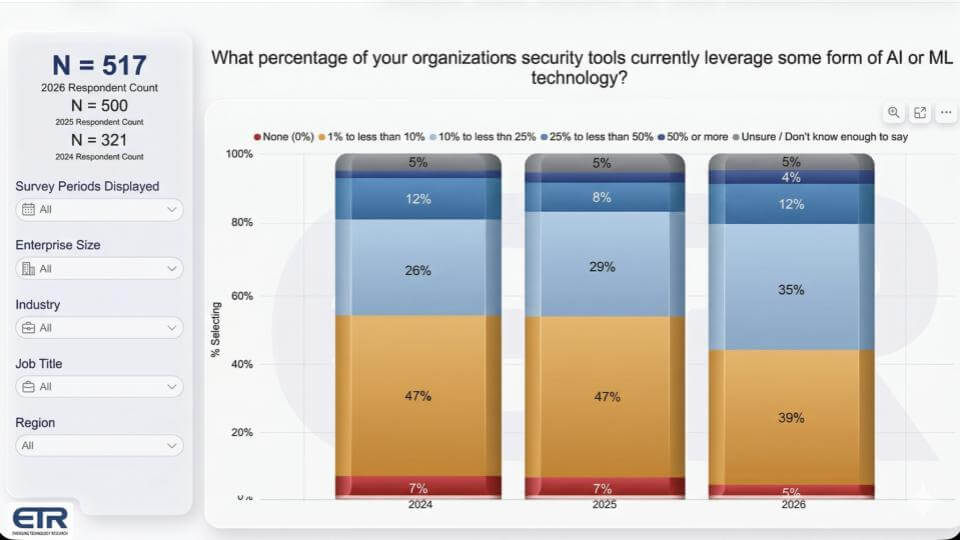
The primary point is that AI is almost ubiquitous. Only 5% of respondents say they should not using any AI in any respect, and that’s likely understated because machine learning has been embedded in security tools for not less than a decade. AI has been present longer than many teams realize.
The more necessary datapoint is we see gradual expansion across the stack:
- Respondents saying AI is utilized in greater than 10% of their security tools rose to 51%, up from 40% last yr.
- Sixteen percent say AI is utilized in greater than half of their security tooling, up from 11%.
So yes, the info suggests AI is steadily being injected into security portfolios. The caveat, nonetheless, is security practitioners are paid to be paranoid. They worry about hallucinations and black-box behavior. They need to know what their products are doing, how AI is characterised, how models are built, and who’s constructing them. Those questions are relevant, especially as agents start taking actions.
The appropriate posture is cautious optimism, in our view. Be skeptical and ask hard questions, but stay open-minded. AI is coming fast and furiously, and organizations that treat it as “optional” will get surprised on the downside.
All the things AI: Governance first, then visibility, then tooling
AI goes to 2026 conferences, and RSAC is not any exception. The issue is the subject is sprawling. Every category has subcategories, and each subcategory has hype. To simplify we assess two tracks – securing AI and defending against AI-enabled threats – then tie it back into an operating plan.
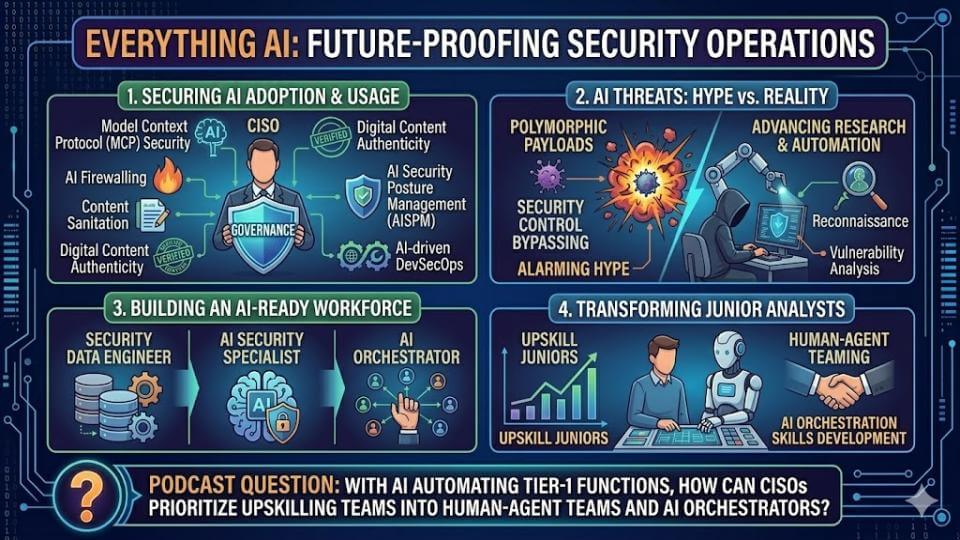
The defender track starts with a reality CISOs reside daily. Executives are gaga over AI – revenue, cost reduction, competitive pressure. The CISO’s job is to say yes, but do it intelligently and manage risk. That’s a careful dance inside most enterprises at once, and it only works if governance is consistent across the corporate.
The sensible sequence we advise is shown below:
- Governance – Establish a framework that’s universally true across the enterprise. Business units need a standard baseline for the way they justify AI use, how they construct AI applications responsibly, and the way they manage bias and risk.
- Visibility – Understand what data is getting used and who’s using it. Shadow AI is the plain issue here. Who’s using AI tools and are they exposing company data? You would like visibility before you may control it.
- Tooling – Once governance and visibility are in place, then herald the controls that implement the principles. That features AI in the event cycle (DevSecOps), identity and liveness checks for biometric-based access, and AI firewalling where rules must be enforced around AI use and AI application development.
AI security just isn’t a single category. MCP security, authentication, provenance, posture management, DevSecOps, SecOps – all of it gets pulled into the conversation since the attack surface is expanding quickly. And a variety of that is being done in co-development with partners and vendors, which adds one other layer of complexity and risk.
On the attacker vector, RSAC might be filled with scary narratives – polymorphic agents, control bypass, more convincing phishing. Much of it’s real. The useful approach is to deal with where the enterprise is definitely exposed today. Specifically, governance gaps, unknown AI usage, weak data controls and inconsistent enforcement. That’s where real budget decisions needs to be made in 2026.
There’s more here than might be unpacked in a single segment, but the important thing point is CISOs must get their hands on this now. AI is moving fast, the attack surface is growing, and the organizations that treat AI governance as a side project will discover quickly that it isn’t.
Tool consolidation vs. platformization: Fewer vendors, more integration, same reality
Tool sprawl has been a recurring theme for years, and the ETR data still reflects how hard it’s to scale back vendors in an actual security stack. The “decrease” bar in red below continues to be tepid – around 10% of respondents say they expect to scale back the variety of cybersecurity vendors over the following 12 months. That hasn’t moved much. The more meaningful delta is the proportion saying they expect to increase vendors has dropped from 51% two years ago to 35% today. That’s “mission completed,” nevertheless it suggests the frantic adoption of shiny recent point tools is slowing.
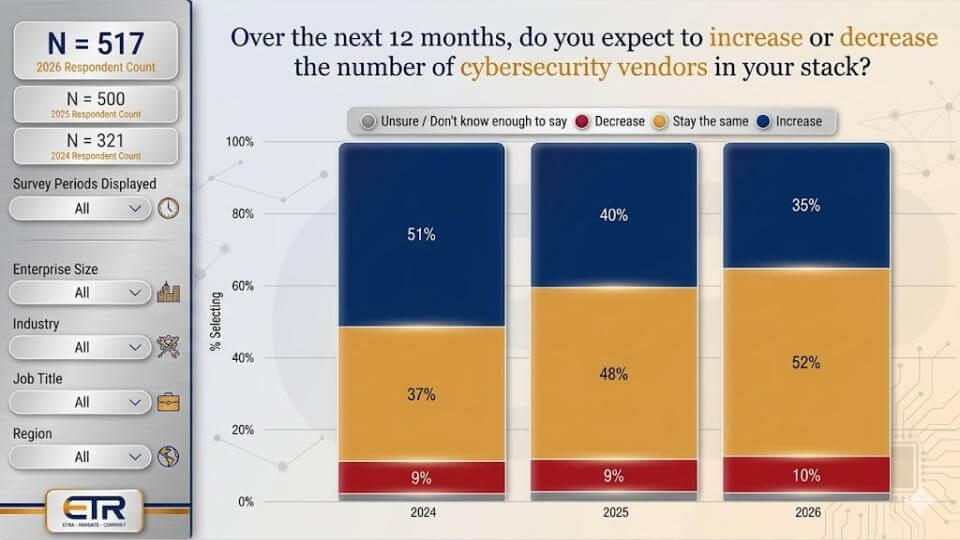
Large enterprises show more movement within the ETR data. Within the Fortune 1000 cut (75 respondents), 16% say they’re decreasing vendors, noticeably higher than the typical. Even there, the larger story is that rationalization is a continuing activity for CISOs – requirements change, tools converge, and teams are at all times asking what might be retired.
There’s also a very important nuance in that vendor consolidation just isn’t the identical as “platformization.”
Vendor consolidation
Vendor consolidation is the “one throat to choke” move. If an environment has CrowdStrike, SentinelOne, Trend Micro, plus legacy Symantec or McAfee, a brand new CISO may simply pick one vendor, standardize and scale skills and operations around that vendor’s product. The advantages are:
- Higher pricing leverage;
- More operational scale for desktop support and SOC teams;
- Fewer consoles and fewer workflows.
That reduces vendor count, nevertheless it doesn’t necessarily create a platform.
Platformization
Platformization is buying diverse tools from a single vendor that has integrated them – threat intelligence, EDR, SIEM, SOAR and other “alphabet soup” capabilities – so the SOC standardizes on a tightly connected set of controls. That approach can work well for small and medium-sized businesses, state and native governments, and any organization with resource constraints. The larger and more diverse the enterprise, the more the platform fit becomes uneven since the environment is customized, the threats vary and global requirements are hard for anybody platform vendor to maintain up with.
Platformization also carries a “platform ecosystem” profit. Major platform vendors bring:
- Partners with custom integrations that stretch the platform;
- Developer tooling and services;
- Skilled services and repair providers that may run the platform in your behalf.
Those are definite benefits, however the platform ceiling is hit in highly heterogeneous global enterprises.
Integration philosophy varies
At the tip of the day, a platform must be tightly integrated. Platforms might be prolonged through application programming interfaces and custom integrations and work pretty much, however the query is whether or not it really works the best way customers want in essentially the most demanding environments. That’s why the acquisitive strategy continues to be a theme in the safety industry. Vendors that buy and integrate argue they do it higher when it’s native – proprietary access to code and deeper engineering integration.
This explains why identity keeps showing up in M&A strategies. Identity because the perimeter isn’t recent, nevertheless it is strategic, and the platform is just nearly as good as its elements. If identity is a core element, platform vendors will either partner deeply or acquire – because weak identity erodes the worth of the remaining of the stack.
The underside line is platformization is real for a segment of the market, consolidation is at all times happening, and innovation still forces recent point tools into the most important enterprises. The most probably near-term final result is more dollars flowing to fewer vendors (industry consolidation), while area of interest innovators still enter where requirements outpace the platforms – then get acquired and absorbed later.
Final thoughts: Zero trust continues to be relevant, as are many other topics
RSAC 2026 goes to be overloaded with topics – zero trust, cloud security, platforms, all of the “DR/CDR/EDR/XDR” alphabet soup, IT/OT, post-quantum and a variety of hallway conversations that find yourself being more helpful than some keynotes. That’s the character of RSAC. The agenda is big, however the lobby con is where people compare notes, determine what’s real and do deals.
The closing segment here focuses on zero trust. It is probably not as sexy because it was a couple of years ago, nevertheless it’s still there and it’s still consuming real cycles. The Department of Defense has something like 156 different categories or descriptions of what makes up zero trust. And CISOs are still in the course of initiatives – not theory, not “we’re excited about it,” but doing energetic work.
The explanation zero trust persists is it cascades into identity, resilience and other parts of the stack. So even though it is probably not the marquee topic on stage, it is going to be within the conversations. Everyone seems to be coping with it, and it’s deeply intertwined with the agent and AI discussions since the minute you progress toward more automation, you would like clearer access control, tighter policy enforcement and higher containment.
RSAC goes to be a full-contact week. The CEO series is back, and theCUBE is survive Media Row in Moscone West. We’ll be exploring the hard questions, comparing practitioner experiences and using the community to sanity-check vendor claims.
Come join us!
Image: theCUBE Research/Gemini
Disclaimer: All statements made regarding firms or securities are strictly beliefs, points of view and opinions held by SiliconANGLE Media, Enterprise Technology Research, other guests on theCUBE and guest writers. Such statements should not recommendations by these individuals to purchase, sell or hold any security. The content presented doesn’t constitute investment advice and shouldn’t be used as the idea for any investment decision. You and only you’re answerable for your investment decisions.
Disclosure: Most of the firms cited in Breaking Evaluation are sponsors of theCUBE and/or clients of theCUBE Research. None of those firms or other firms have any editorial control over or advanced viewing of what’s published in Breaking Evaluation.
Support our mission to maintain content open and free by engaging with theCUBE community. Join theCUBE’s Alumni Trust Network, where technology leaders connect, share intelligence and create opportunities.
- 15M+ viewers of theCUBE videos, powering conversations across AI, cloud, cybersecurity and more
- 11.4k+ theCUBE alumni — Connect with greater than 11,400 tech and business leaders shaping the longer term through a singular trusted-based network.
About SiliconANGLE Media
Founded by tech visionaries John Furrier and Dave Vellante, SiliconANGLE Media has built a dynamic ecosystem of industry-leading digital media brands that reach 15+ million elite tech professionals. Our recent proprietary theCUBE AI Video Cloud is breaking ground in audience interaction, leveraging theCUBEai.com neural network to assist technology firms make data-driven decisions and stay on the forefront of industry conversations.