Online data is mostly pretty secure. Assuming everyone seems to be careful with passwords and other protections, you’ll be able to consider it as being locked in a vault so strong that even all of the world’s supercomputers, working together for 10,000 years, couldn’t crack it.
But last month, Google and others released results suggesting a brand new sort of computer—a quantum computer—might have the opportunity to open the vault with significantly fewer resources than previously thought.
The changes are coming on two fronts. On one, tech giants akin to IBM and Google are racing to construct ever-larger quantum computers: IBM hopes to realize a real advantage over classical computers in some special cases this yr, and a good more powerful “fault-tolerant” system by 2029.
On the opposite front, theorists are refining quantum algorithms: Recent work shows the resources needed to interrupt today’s cryptography could also be far fewer than earlier estimates.
The online result? The day quantum computers can break widely used cryptography—portentously dubbed “Q-Day”—could also be approaching faster than expected.
The Quantum Hardware Race
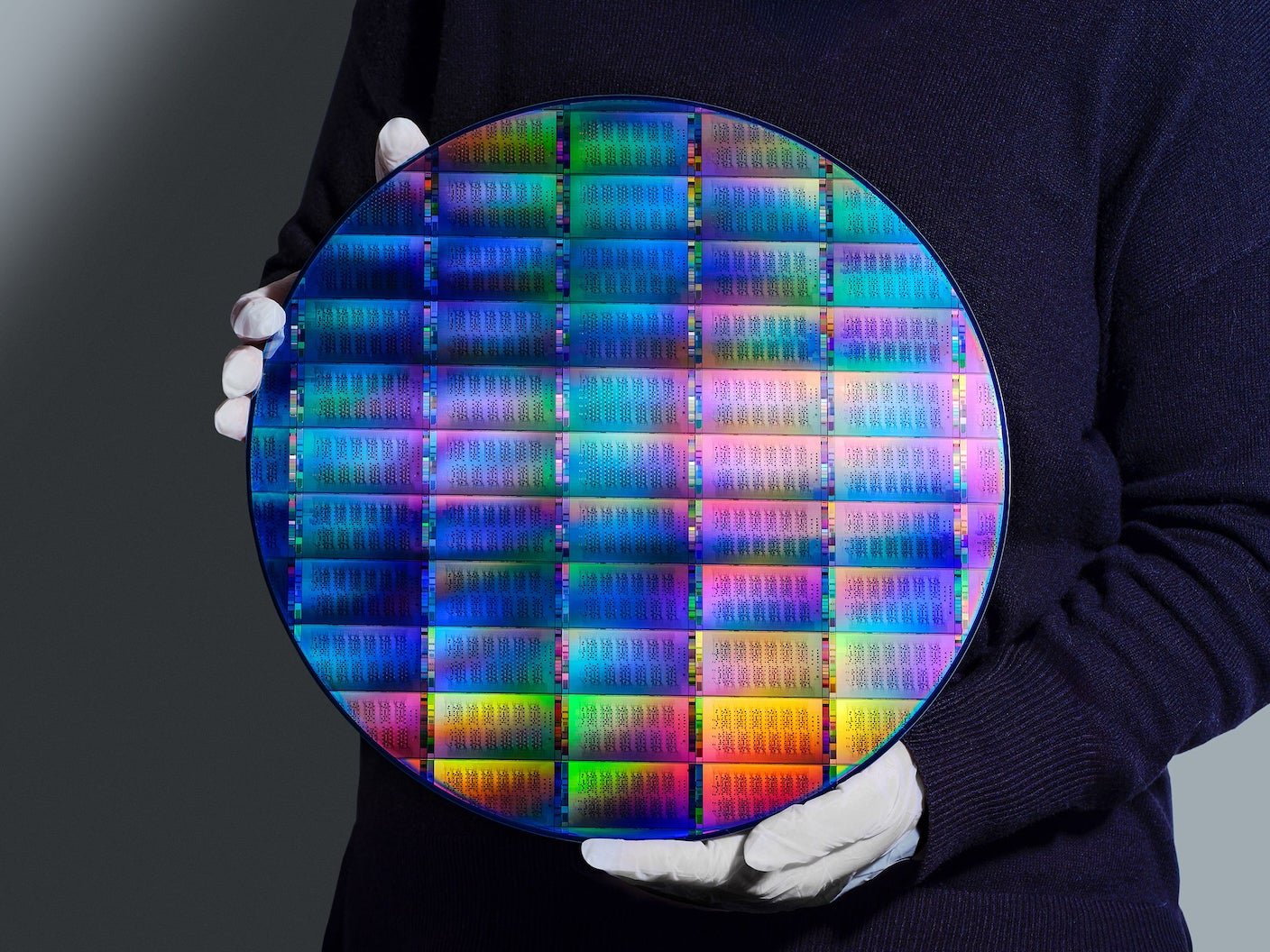
Quantum computers are built from quantum bits, or qubits, which use the counterintuitive properties of very tiny objects to perform computations in a special and sometimes much more efficient way from traditional computers.
Up to now the technology is in its infancy, with the key goal to extend the variety of qubits that may be connected to work as a single computer. Greater quantum computers ought to be a lot better at some things than their traditional counterparts—they’ll have a “quantum advantage.”
Late last yr, IBM unveiled a 120-qubit chip which it hopes will exhibit a quantum advantage for some tasks.
Google also recently announced it planned to hurry up its move to adopt encryption techniques that ought to be protected against quantum computers, often known as post-quantum cryptography.
Alongside these tech giants, newer approaches are also flourishing. PsiQuantum is using light-based qubits and traditional chip-manufacturing technology. Experimental platforms akin to neutral-atom systems have demonstrated control over 1000’s of qubits in laboratory settings.
In response, standards bodies and national agencies are setting increasingly concrete timelines for moving away from common encryption systems which are vulnerable to quantum attack.
In america, the National Institute of Standards and Technology (NIST) has proposed a transition away from quantum-vulnerable cryptography, with migration largely accomplished by 2035. In Australia, the Australian Signals Directorate has issued similar guidance, urging organizations to start planning immediately and transition to post-quantum cryptography by 2030.
Algorithms Make the Lock-Picking Faster
Hardware is just half the story. Equally vital are advances in quantum algorithms—ways to make use of quantum computers to attack encryption.
Much interest in quantum computer development was spurred by Peter Shor’s 1994 discovery of an algorithm that showed how quantum computers could efficiently find the prime aspects of very large numbers. This mathematical trick is precisely what you want to break the common RSA encryption method.
For many years, it was believed a quantum computer would wish tens of millions of physical qubits to pose a threat to real-world encryption. This is much larger than current systems, so the threat felt comfortably distant.
That picture is now changing.
In March 2026, Google’s Quantum AI team released an in depth study showing that far fewer resources could also be needed to attack a special sort of encryption which uses mathematical objects called elliptic curves. That is what systems including Bitcoin and Ethereum use—and the study shows how a quantum computer with fewer than half 1,000,000 physical qubits may have the opportunity to crack it in minutes.
That’s still a great distance beyond current quantum computers, but around ten times lower than earlier estimates.
At the identical time, a March 2026 preprint from a Caltech—Berkeley—Oratomic collaboration explores what is likely to be possible using neutral-atom quantum computers. The researchers estimate that Shor’s algorithm could possibly be implemented with as few as 10,000–20,000 atomic qubits. In a single design they propose, a system with around 26,000 qubits could crack Bitcoin’s encryption in a couple of days, while tougher problems just like the RSA method with a 2048-bit key would wish more time and resources.
In plain terms: The codebreakers have gotten more efficient. Advances in algorithms and design are steadily lowering the bar for quantum attacks, even before large-scale hardware exists.
What Now?
So what does this mean in practice?
First, there isn’t a immediate catastrophe—today’s cryptography won’t be broken overnight. However the direction of travel is evident. Each improvement in hardware or algorithms reduces the gap between current capabilities and useful quantum cracking machines.
Second, viable defenses exist already. NIST has standardized several post-quantum cryptographic algorithms that are believed to be immune to quantum attacks.
Technology firms have begun deploying these in hybrid modes: Google Chrome and Cloudflare, for instance, already support post-quantum protections in some protocols and services.
Systems that rely heavily on elliptic-curve cryptography—including cryptocurrencies and lots of secure communication protocols—will need particular attention. Google’s recent work explicitly highlights the necessity to migrate blockchain systems to post-quantum schemes.
Finally, it is a two-front race. It is just not enough to trace progress in quantum hardware alone. Advances in algorithms and error correction may be just as vital, and up to date results show these improvements can significantly reduce the estimated cost of attacks.
Every recent headline about reduced qubit counts or faster quantum algorithms ought to be understood for what it’s: one other step toward a future where today’s cryptographic assumptions not hold.
The one reliable defense is to maneuver—deliberately but decisively—toward quantum-safe cryptography.